Chrome DBSC: Shift from Bearer Cookies to device-bound Session credentials
 Most authentication systems are built around a comforting illusion: once a user successfully logs in, the system believes it knows who is on the other side of the connection.
Most authentication systems are built around a comforting illusion: once a user successfully logs in, the system believes it knows who is on the other side of the connection.
In reality, most web applications do not continuously know who is using the session. They know only that each request carries a valid cookie.
That distinction is not academic. It is the reason session theft remains one of the most effective ways to bypass passwords, MFA, passkeys, risk checks, and even carefully designed identity-provider flows.
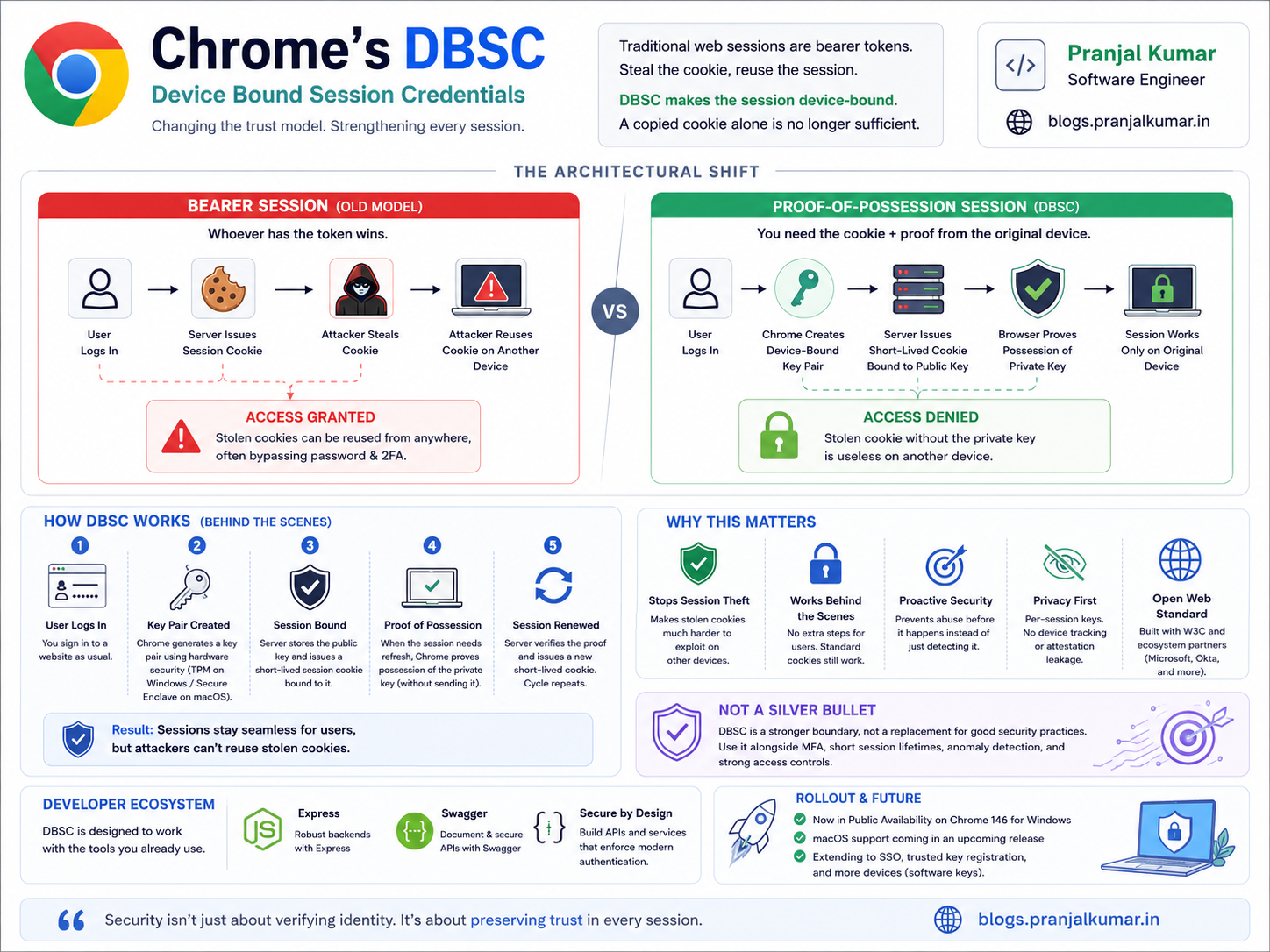
Chrome's Device Bound Session Credentials, commonly called DBSC, is aimed directly at this weakness. It changes the trust model of web sessions from:
Bearer session model:
If you have the cookie, you are the session.
To:
Device-bound proof-of-possession model:
If you have the cookie, you must also prove you are still on the original device.
That is a fundamental architectural shift.
DBSC is not just another browser feature. It is part of a broader movement away from portable bearer credentials and toward credentials that are bound to context, device, and proof of possession.
The core problem: cookies are bearer credentials
A traditional session cookie is a bearer credential. “Bearer” means possession is enough.
The server does not ask:
- Why does this requester have the cookie?
- Was this cookie copied from another machine?
- Is this the same browser that originally authenticated?
- Is the private device context still present?
If the cookie is valid and unexpired, the request is generally treated as authenticated.
That gives us a simple but dangerous flow:
User logs in with password + MFA
↓
Server issues session cookie
↓
Malware steals cookie
↓
Attacker imports cookie elsewhere
↓
Server accepts attacker as logged-in user
This is why cookie theft can bypass MFA. MFA protects the login ceremony, but once a session has been established, the cookie often becomes the real proof of authentication.
The attacker does not need to defeat cryptography. They do not need to brute-force a password. They do not need to intercept a one-time password. They only need the browser's already-issued session artifact.
That is why infostealer malware is so effective. It targets browser session state, extracts cookies or tokens, and replays them elsewhere.
The uncomfortable truth is this:
If a credential is portable, attackers will build an economy around stealing and replaying it.
DBSC exists because the web's dominant session model made authenticated sessions too easy to move from one device to another.
DBSC's big idea: make the session non-portable
DBSC does not try to make cookies impossible to steal. That would be unrealistic.
If malware runs with sufficient access on a user's machine, it may still be able to read browser-accessible state, observe network activity, or abuse the active browser context.
Instead, DBSC attacks the attacker's next step: replay.
The goal is not:
No attacker can ever copy a cookie.
The goal is:
A copied cookie should not be enough to continue the session from another machine.
DBSC does this by binding session continuity to a cryptographic key pair generated on the user's device.
At a high level:
- Chrome creates a public/private key pair for the session.
- The private key remains protected on the device.
- The server stores the public key.
- The server issues short-lived cookies.
- When the cookie needs renewal, Chrome proves possession of the private key.
- If proof succeeds, the server issues a fresh short-lived cookie.
So the new session equation becomes:
Valid continued session = short-lived cookie + proof of device-held private key
That is the core DBSC idea.
The attacker may steal the cookie, but once that short-lived cookie expires, they cannot renew the session from another machine unless they can also prove possession of the original device-bound private key.
How DBSC works: the actual flow
DBSC introduces three important backend concepts:
- Session registration
- Short-lived cookies
- Refresh with proof of possession
The important design choice is that DBSC is additive. Applications do not need to rewrite every endpoint to understand a brand-new authentication system. Instead, DBSC is concentrated around login, registration, and refresh.
Most application endpoints can continue checking cookies as they already do.
Step 1: user logs in normally
The user authenticates using the site's existing login mechanism:
- Password
- MFA
- Passkey
- SSO
- Enterprise identity provider
- Any existing authentication flow
DBSC does not replace initial authentication. It strengthens what happens after authentication.
That distinction matters.
Passkeys and MFA answer:
Can this user authenticate now?
DBSC answers:
Can this already-authenticated session still prove it belongs to the original device?
Those are related, but different, security questions.
Step 2: server asks Chrome to start a device-bound session
After login, the server sends a DBSC registration instruction using an HTTP response header such as:
Secure-Session-Registration: ...
Conceptually, the server is telling Chrome:
For this authenticated session, create a device-bound credential and register it with me.
This is the bootstrap step.
Step 3: Chrome generates a public/private key pair
Chrome generates a new asymmetric key pair for the session.
Public key → sent to server
Private key → protected on the device
The public key is not secret. The server stores it and later uses it to verify signatures.
The private key is the important artifact. It should not be exportable like a normal file. Ideally, it is protected by hardware-backed security such as a TPM on Windows or Secure Enclave-style protection on macOS.
Step 4: Chrome registers the public key
Chrome calls the site's registration endpoint and sends the public key and related session material.
The server may store records similar to:
user_id
session_id
public_key
refresh_endpoint
cookie_scope
registration_time
expiration_policy
risk_policy
The private key never leaves the device.
Step 5: server issues short-lived cookies
This is one of the most important parts of DBSC.
The server should not continue issuing long-lived bearer cookies. Instead, it transitions to short-lived cookies.
The point is not that cookies become impossible to steal. The point is that stolen cookies become much less valuable because they expire quickly and cannot be refreshed without the device-bound private key.
The model changes from:
Long-lived bearer cookie
To:
Short-lived cookie + hardware-backed/session-bound renewal
Step 6: Chrome refreshes the session with proof of possession
When Chrome needs to make a request and notices that the DBSC-controlled cookie is missing or expired, Chrome can pause the original request and call the configured refresh endpoint.
The refresh flow looks like this:
Original request needs valid cookie
↓
Cookie expired or missing
↓
Chrome calls refresh endpoint
↓
Server returns challenge
↓
Chrome signs challenge using device-held private key
↓
Server verifies signature using stored public key
↓
Server issues fresh short-lived cookie
↓
Original request resumes
This lets the user experience remain smooth while session continuation becomes cryptographically bound to the original device.
That is the beauty of DBSC: it adds a stronger trust boundary without turning every session renewal into a visible user challenge.
Why DBSC is not just "shorter cookie expiry"
A natural question is:
Why not just make all session cookies expire every five minutes?
Because short expiry alone creates a usability problem.
If cookies expire too quickly, users are constantly forced to reauthenticate. To avoid that, most systems introduce a long-lived refresh token or long-lived session cookie.
But then the refresh artifact becomes the new bearer credential.
Short-lived access cookie + long-lived bearer refresh token
If malware steals the refresh token, the attacker can continue minting new session cookies.
DBSC changes that equation.
Traditional refresh:
Refresh token is a bearer credential.
DBSC refresh:
Refresh requires proof of possession of a device-held private key.
This is a materially better security/usability tradeoff.
Users do not need to log in repeatedly, but attackers cannot simply copy the refresh capability to another machine.
The role of TPM: the hardware root of trust
The TPM is one of the most important pieces of the DBSC story.
A Trusted Platform Module, or TPM, is a hardware-backed cryptographic component designed to generate, protect, and use cryptographic keys. It can create keys whose private material is difficult or impossible to export through ordinary software APIs.
For DBSC, the browser needs a private key with three properties:
- It is generated on the user's device.
- It is difficult to export.
- It can sign server challenges when session refresh is required.
That is exactly the kind of problem TPMs are designed to support.
Why software key storage is not enough
Imagine Chrome generated a DBSC private key and stored it as a normal file:
~/Chrome/Profile/DBSC/private-key.pem
That would not meaningfully solve cookie theft.
The same malware that steals cookies could steal the private key file too.
Then the attacker would have:
stolen cookie + stolen private key = replayable session
At that point, DBSC would collapse back into a bearer-like model.
The key cannot merely be “local.” It must be protected in a way that makes extraction hard.
This is where TPM-backed storage matters.
A TPM-backed key behaves conceptually like this:
Application: Please sign this challenge.
TPM: Here is the signature.
Application: Please give me the private key.
TPM: No.
The browser can use the key, but it cannot casually export the raw private key material.
TPM as a signing oracle
In DBSC, the TPM-backed key does not need to decrypt data or reveal secrets. It primarily needs to sign challenges.
The flow is conceptually:
Server creates challenge:
nonce + session_id + timestamp + origin context
Chrome asks protected key:
sign(challenge)
Chrome sends to server:
challenge + signature
Server verifies:
verify(public_key, challenge, signature)
If verification succeeds, the server knows that the client can still access the original device-bound private key.
What TPM proves — and what it does not
This nuance is critical.
TPM-backed DBSC proves:
The session can still access the original device-bound key.
It does not prove:
The device is malware-free.
The user is physically present.
The browser process is uncompromised.
The OS is fully trustworthy.
If malware is running on the same machine and can control the browser or trigger signing operations, it may still abuse the active session locally.
This is sometimes called the signing oracle problem.
A non-exportable TPM key prevents this:
Export private key → use it anywhere
But it may not fully prevent this:
Compromised local device → ask browser/TPM to sign challenge locally
So DBSC changes the attacker's path.
Before DBSC:
Steal cookie → replay anywhere
After DBSC:
Steal cookie → short-term access only
Need original device key → must compromise or operate from original device
That is still a huge improvement.
It turns a scalable remote replay attack into a harder local compromise problem.
DBSC attacks the infostealer business model
DBSC should not be understood only as a browser feature. It should be understood as an economic attack against infostealer malware.
Infostealers are profitable because session credentials are portable.
A typical attacker workflow looks like this:
Compromise endpoint
↓
Extract browser cookies
↓
Upload cookies to attacker infrastructure
↓
Sell or replay sessions
↓
Bypass MFA because login already happened
The scalability comes from portability. Once a cookie is stolen, the attacker can use it elsewhere.
DBSC reduces that value.
With DBSC:
Cookie stolen today
↓
Cookie works only until short-lived expiry
↓
Attacker cannot refresh without original device-bound private key
This does not make attacks impossible, but it damages the attacker's return on investment.
That is what good security architecture often does. It does not merely block one technique; it changes the economics of the attack.
DBSC vs DPoP: same philosophy, different layer
DBSC belongs to a broader family of proof-of-possession and sender-constrained credential systems.
OAuth DPoP, standardized in RFC 9449, follows a similar principle for OAuth tokens. Instead of allowing a token to be used by anyone who possesses it, DPoP binds token usage to proof that the client possesses a private key.
The comparison looks like this:
Bearer token:
token alone is enough
DPoP:
token + proof of private key required
DBSC:
cookie + proof of device-bound private key required
The philosophy is the same: make stolen credentials harder to replay.
The difference is where they operate.
DPoP is primarily an OAuth/API token mechanism.
DBSC is a browser/session-cookie mechanism.
That makes DBSC especially relevant for traditional web applications that still rely heavily on cookies and browser-managed session state.
Why earlier Token Binding ideas struggled
DBSC is not the first attempt to bind credentials to a client.
Earlier approaches, such as Token Binding, tried to bind tokens at the TLS layer. The idea was elegant: cryptographically bind tokens to the TLS connection so stolen tokens could not be replayed elsewhere.
But deployment reality made this hard.
Modern web infrastructure often looks like this:
Browser
↓ TLS
CDN / edge proxy
↓ internal routing
Load balancer
↓
API gateway
↓
Service mesh
↓
Application service
↓
Auth/session store
The service that owns the session may not be the component terminating the original TLS connection.
If the proof is too low in the stack, application teams may not be able to reliably consume it.
DBSC is more pragmatic because it operates closer to HTTP and application session semantics. The auth system that issues and refreshes cookies can also verify device proof.
That is good architecture: put the security control where the ownership boundary actually exists.
DBSC and privacy: avoiding the supercookie trap
Any device-binding mechanism immediately raises a privacy concern:
Are we creating a stable device identifier?
If every website received the same hardware-backed public key, DBSC would become a tracking disaster.
Sites could correlate users across origins and sessions.
A responsible design must avoid that.
DBSC's design uses session-specific keys rather than exposing a universal device identity. The goal is to bind this session to this device, not reveal a stable global hardware identity.
The difference is huge.
Good design:
Site A session key ≠ Site B session key
Session 1 key ≠ Session 2 key
No global device identifier exposed
Bad design:
Same public key exposed everywhere
Device becomes trackable across the web
Security features that create persistent tracking surfaces will face resistance from browsers, users, regulators, and privacy engineers.
DBSC is interesting because it tries to improve session security without turning the browser into a device-identification oracle.
What DBSC actually stops
DBSC is strongest against off-device replay.
It helps when the attacker flow is:
Malware steals cookie
↓
Attacker imports cookie into another browser/device
↓
Attacker tries to continue the session
DBSC breaks this flow because the attacker does not have the original device-bound private key needed to refresh the session.
It also improves defender visibility.
If attackers can no longer replay cookies from their own infrastructure, they may be forced to act from the compromised user's device. That makes endpoint detection, enterprise device management, browser telemetry, and cleanup more relevant.
In security terms, DBSC converts a portable credential problem into a device-compromise problem.
That is not perfect, but it is meaningfully better.
What DBSC does not stop
A serious engineering analysis must be clear about boundaries.
DBSC does not fully stop:
- Malware actively controlling the browser on the same device.
- Remote access trojans operating through the victim's browser.
- Malicious browser extensions acting inside the browser context.
- XSS that performs actions through the user's active session.
- Phishing that causes the user to establish a fresh attacker-controlled session.
- Attacks during or before DBSC registration.
- Server-side session-store compromise.
- Local malware using the device as a signing oracle.
This does not make DBSC weak. It makes its threat model precise.
DBSC is an anti-exfiltration and anti-replay control. It is not a complete endpoint integrity solution.
The correct mental model is:
DBSC does not prove the user is safe.
DBSC proves the session can still access the original device-bound key.
That is still extremely valuable.
DBSC and passkeys: different stages of trust
People may confuse DBSC with passkeys because both use public/private key cryptography and device-associated keys.
But they solve different problems.
Passkey:
Can this user authenticate to this account?
DBSC:
Can this already-authenticated session still prove it belongs to the original device?
Passkeys protect the front door.
DBSC protects the session after the user has entered.
A strong modern authentication architecture should combine both:
Passkey login
+
Device-bound session renewal
+
Short-lived cookies
+
Risk-based step-up authentication
+
Session revocation
+
Endpoint posture and detection
That is the direction web authentication is moving: fewer reusable secrets and more contextual proof.
DBSC and "password sharing"
The YouTube video framing around DBSC and password/session sharing is understandable.
If session state is no longer portable across machines, then copying a logged-in browser profile or cookie jar to another device becomes less useful.
In that sense, DBSC can make casual session sharing harder.
But from a security engineering perspective, password sharing is not the deepest point.
The deeper point is:
Attackers should not be able to cheaply replay stolen authenticated sessions at scale.
For consumer subscription services, DBSC may also help enforce that sessions remain tied to legitimate devices. But if DBSC is marketed only as anti-sharing, users may perceive it as restrictive DRM.
The stronger and more accurate framing is session theft protection.
How an enterprise auth team should implement DBSC
If I were designing DBSC adoption for a large-scale company, I would not let every product team independently bolt it onto its own application.
I would centralize it in the authentication platform.
A mature architecture would look like this:
Identity Provider / Auth Gateway
↓
DBSC registration service
↓
DBSC refresh service
↓
Session store / public key registry
↓
Risk engine
↓
Observability + security analytics
Registration service responsibilities
The registration service should:
- Validate that the user recently completed legitimate authentication.
- Accept and store the DBSC public key.
- Bind the public key to a specific session.
- Define cookie scope and refresh policy.
- Transition the user from bootstrap session to short-lived bound cookies.
- Emit security logs for registration events.
Refresh service responsibilities
The refresh service is even more critical.
It should:
- Generate unpredictable challenges.
- Validate signed responses.
- Reject stale challenges.
- Reject replayed challenges.
- Rotate short-lived cookies.
- Integrate with session revocation.
- Feed suspicious proof failures into the risk engine.
- Support controlled fallback for unsupported browsers or devices.
Observability requirements
A DBSC rollout without observability is dangerous.
Teams need dashboards for:
DBSC registration success rate
DBSC refresh success rate
Refresh latency
Proof validation failures
Fallback frequency
Unsupported browser/device percentage
Sessions still using long-lived bearer cookies
Suspicious repeated refresh failures
DBSC turns the refresh path into part of the authentication control plane. It must be designed with the same seriousness as login infrastructure.
Backend architecture pattern
A clean backend design treats DBSC as a session-hardening layer.
┌────────────────────┐
│ User authenticates │
└─────────┬──────────┘
│
▼
┌──────��─────────────────┐
│ Auth service issues │
│ registration header │
└─────────┬─────────────┘
│
▼
┌───────────────────────┐
│ Browser creates key │
│ TPM/Secure Enclave │
└─────────┬─────────────┘
│
▼
┌───────────────────────┐
│ Registration endpoint │
│ stores public key │
└─────────┬─────────────┘
│
▼
┌───────────────────────┐
│ Short-lived cookie │
│ issued │
└─────────┬─────────────┘
│
▼
┌───────────────────────┐
│ Refresh endpoint │
│ verifies signed proof │
└───────────────────────┘
For high-scale systems, the refresh endpoint must be:
- Multi-region
- Low latency
- Highly available
- Rate limited
- Replay resistant
- Audited
- Compatible with CDNs and reverse proxies
- Integrated with risk scoring
- Integrated with session revocation
If the refresh service goes down, users may appear logged out even if the main application is healthy.
That makes DBSC infrastructure part of the critical path.
Risk-based policy decisions
DBSC creates new security signals. The question is what the server should do with them.
For example:
DBSC proof succeeds:
Continue session normally.
DBSC proof fails once:
Retry or gracefully degrade.
DBSC proof repeatedly fails:
Trigger step-up authentication.
DBSC proof fails from suspicious context:
Revoke session and alert.
DBSC unavailable on device:
Use shorter session lifetime and stronger risk checks.
This is where DBSC becomes more than protocol plumbing. It becomes part of adaptive access control.
A mature system should not treat every failure identically. Some failures are benign: browser updates, device migration, corrupted profile state, unsupported hardware, enterprise policy restrictions.
Other failures may be suspicious: repeated refresh attempts, impossible travel, mismatched device posture, or refresh attempts after known compromise.
The policy layer matters as much as the cryptography.
The real architectural insight
The real lesson from DBSC is bigger than Chrome.
For decades, web security has over-weighted the login moment and under-weighted the session lifetime.
Most systems ask:
Did the user authenticate correctly at time T0?
Attackers increasingly operate after T0.
They wait until the user is already authenticated, steal the resulting session, and bypass the expensive login security controls.
Modern security needs to ask better questions:
Should this session still be trusted now?
Is it still on the original device?
Has the risk posture changed?
Can the client prove possession of the original key?
Should this action require step-up authentication?
DBSC is valuable because it moves web sessions toward continuous trust validation without constantly annoying the user.
That is the future of authentication: not more prompts, but stronger invisible guarantees.
Final takeaway
DBSC is not the death of cookies.
It is the hardening of cookies.
It does not replace MFA. It does not replace passkeys. It does not replace endpoint security. It does not prove the device is uncompromised.
But it fixes one of the worst properties of web sessions:
A stolen cookie should not be a portable identity.
By using device-bound cryptographic keys, ideally protected by TPM or similar hardware-backed mechanisms, DBSC makes session renewal depend on proof from the original device.
The old model was:
Trust follows the cookie.
The DBSC model is:
Trust follows the cookie only while the original device can prove possession.
That is not a small implementation detail. That is a better trust boundary.
And in security architecture, better trust boundaries are how the game actually changes.
References
- Chrome Developers: Device Bound Session Credentials
- Google Security Blog: Fighting cookie theft using device bound sessions
- WICG DBSC Explainer
- W3C Draft: Device Bound Session Credentials
- RFC 9449: OAuth 2.0 Demonstrating Proof of Possession
- Microsoft: Trusted Platform Module Technology Overview
- OWASP Session Management Cheat Sheet
- YouTube reference video